How are WLAN Infrastructures in Enterprises Secured?
Learn about the scalability challenges of Pre-shared (PSK) configurations in the enterprise, as well as how 802.1X addresses and resolves them elegantly.

Hello World! In previous posts, you learnt about personal networks with security up to WPA2. From now on, I'll be discussing Enterprise networks with you and popular attacks on them. For educational purposes, of course 😏.
Before moving forward, you should know about the limitations of the personal network in corporate.
Personal Networking Issues in the Workplace
Let's say you hired workers, but after a while, you forced them to leave or fired them due to certain problems. Initially, they required to access the resources on your network, so you had shared the pre-shared key with them to setup their mobile devices. After they will leave the organisation, they might leak this key or become victim of client based (passive) attacks which could lead to retrieving of this PSK.
You're doomed now! Anyone sitting in the parking area has access to your internal network. If the breach is detected in your organisation, all legitimate devices will need to be re-authenticated with a new PSK, which will cause some disruption in the business operations.
It becomes worse when you will realise that identifying culprit becomes even more difficult. Based on the given circumstances, the suspect is the one who left the organisation, but the culprit could still be working for you. This is another challenge for a company to overcome in order to eliminate future potential risks.
By now, it's obvious that we require dynamic control over the creation of authentication credentials for users, as well as an administration panel to manage these and revoke access when users leave the organisation. This is one of the issues addressed by the IEEE 802.1X Standard and RADIUS protocol. This method improves network security by allowing for individualised and time-limited access, which reduces the risk associated with static PSKs.
Let's learn more about it, now!
The 802.1X Standard
802.1X is just a standard, which lets you configure port-based network access control (PNAC) in the organisation using Extended Authentication Protocol (EAP) to enable per-user authentication mechanism. It was released about two years before WPA, initially for Local Area Networks (LANs), but was later in year 2004 expanded to include WLAN by the IEEE 802.11 work group. There are in fact, multiple revisions to the standard like adding more security features.

Under the hood, 802.1X uses RADIUS and EAP to facilitate the authentication mechanism. Therefore, in terms of Operating Systems, 802.1X defines the policy, whereas RADIUS and EAP are the mechanisms to implement that policy.
Even if you are a student, you may have used this in your university/college. Recall when you need to authenticate your devices before accessing internal journals or the internet you need to enter your username and password to some login page (captive portal).
Port? You mean TCP...?
Wait 🛑! Do not mix up the TCP port and the 802.1X port. They are both implemented at different layers of the OSI model. In this context, the term port refers to the physical port (OSI Layer 2) on the network device, such as switch or the access point.
Access control at port refers to the process whereby authentication and authorisation take place at the physical port of the network devices. The device will be granted access to the network behind a network device (access point in this context) if and only if it has successfully completed the port authentication. Think of it as the bouncers only opening the club door for you if certain requirements are met. So when your credentials are invalid, you will be dissociated from the network and won't be able to send further frames to it.
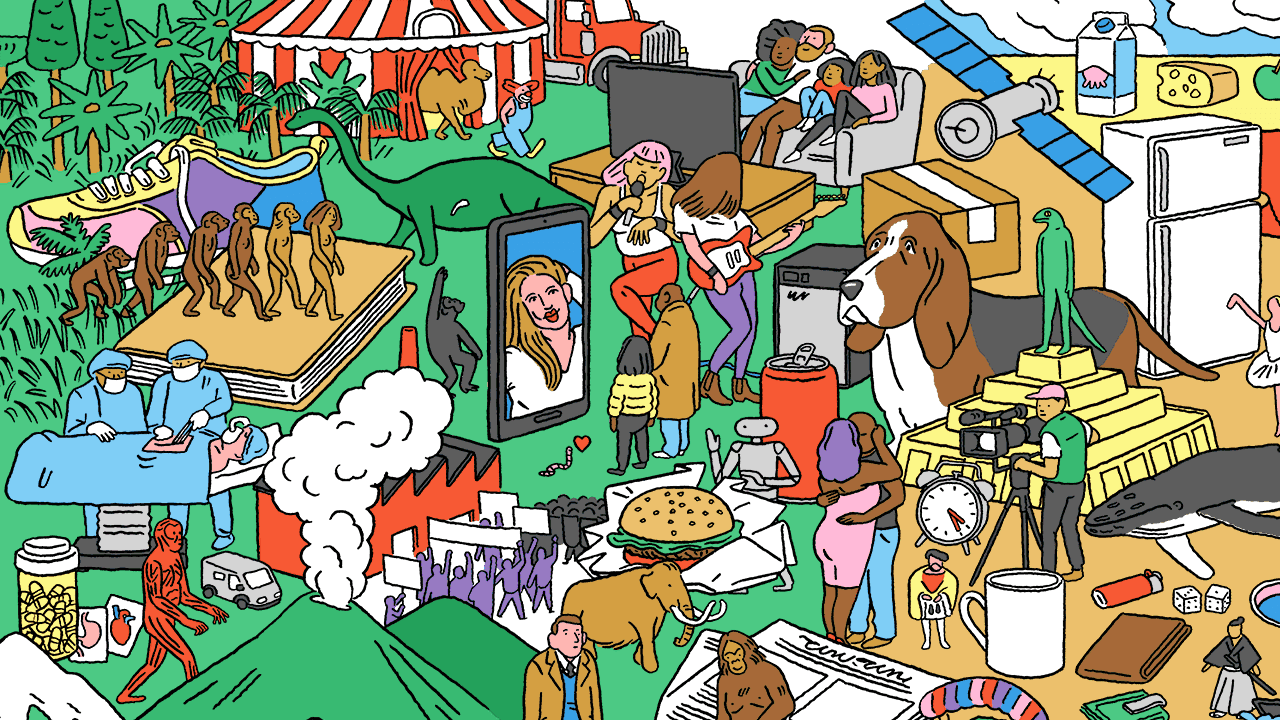
802.1X Architecture
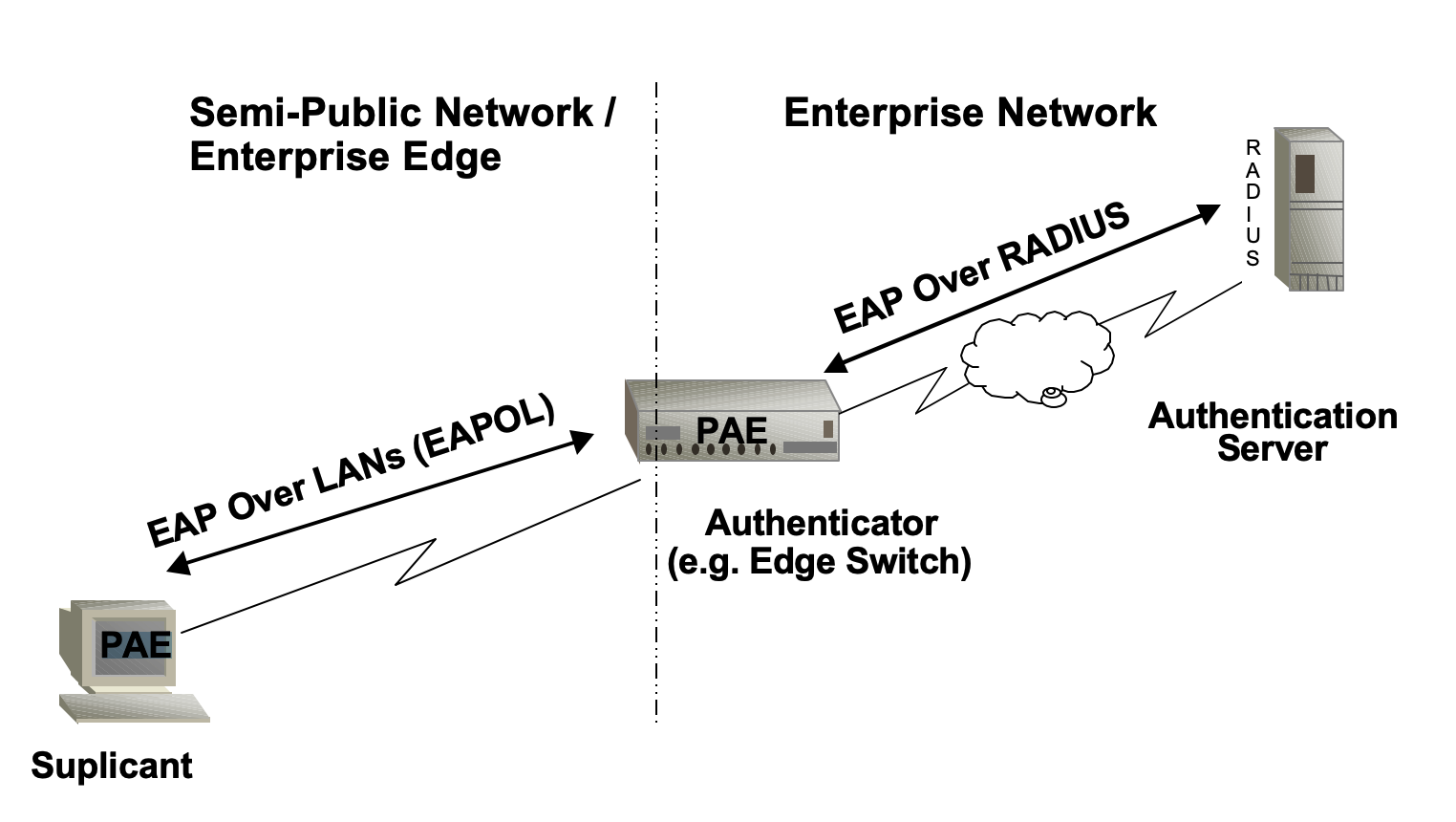
There are 3 actors involved in the authentication process:
- Supplicant, is the client device requesting for the access on the network. It can also be used interchangeably to refer to the software running on the client that provides credentials to the authenticator.
- Authenticator, is a network device that provides a data link between the client and the network and can allow or block network traffic between the two, such as an Ethernet switch or wireless access point.
- Authenticator Server, is typically a trusted server that can receive and respond to requests for network access, and can tell the authenticator whether the connection is to be allowed, or not. This is where RADIUS and EAP protocols compliant softwares run.

Authenticators are installed throughout the area and connected to the authentication server, which is typically centrally located in the administration department in a widely distributed corporate setting. After that, the authenticators act as a go-between for the supplicants and the authentication server.
The connecting device does not have network connectivity until authentication is successful. Because it cannot connect to the authentication server directly, the authenticator is used as the Bifrost.
The supplicant must first provide the required credentials to the authenticator, which could be either username/password or certificates; you (as an IT admin) have the final say, EAP got you covered. This is how user's identity is determined on the network, and often this information is used with telemetry and logging.
Controlled vs Uncontrolled Ports Entities
You're probably wondering how, if the user can only access the network after being authenticated, the authentication frames are exchanged with the AAA server, which is located in the enterprise's network. That is accomplished via a special port known as uncontrolled port, which allows the flow of of unauthenticated frames (involved before supplicant is authenticated).

A controlled port is another port entity that is used for secure communication. It is managed by the 802.1X PAE (Port Access Entity) which allows or prevents network ingress/egress based on the authentication state of the supplicant. The supplicant is promoted to this port entity once it has been authenticated.
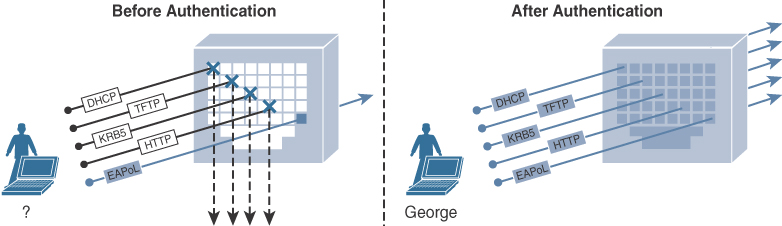
A Port Access Entity (PAE) is a network security concept which enforces access control at network ports, functioning as either a supplicant (seeking network access) or an authenticator (controlling access based on authentication). It ensures secure network access by verifying identities before granting permissions.
In fact, you can use dot1x toolkit from Cisco to configure the port rule. It also supports both mode, where the port behaves as both supplicant and authenticator.
dot1x pae [supplicant | authenticator | both]Configure the current port to specific role

Where does EAP sit in this Set up?
EAP is a port agnostic (same methods works for both wired and wireless) authentication framework which provides a set of methods to facilitate the secure exchange of authentication messages through medium, similar to how you use different methods on a web page to authenticate users. Because it defined some rules like some frameworks (C++/Boost, Python/Django, Node.js/Express and etc), we also call it a protocol.
Because EAP only facilitates the authentication mechanism, it is always carried by another protocol. I will be discussing its encapsulation in the RADIUS frames in the next post.


When the EAP is deployed on the local area networks, and its packets are carried by protocols defined for LANs, it becomes EAPoL (EAP over LAN). You will see EAPOL (802.1X Architecture) protocol type in the Wireshark when supplicant is exchanging the keys with the authenticator after success message from the EAP phase.

After EAP phase succeeds, the authenticator and supplicant carries out 4-way key handshake process for establishing the WPA2 encryption. The reason is same as choosing EAP – why build another encryption, if you can use the existing stack.

The PMK is generated from the previous EAP steps. Unlike the PSK mode, the RADIUS server will provision ephemeral PMKs, which are generally valid for the specific sessions, so even if keys are compromised, they will become invalid later on.
Conclusion
In conclusion, ensuring the security of enterprise Wi-Fi networks is crucial for protecting sensitive information and maintaining network reliability. Throughout our discussion, we have learnt how using PSK in the workplace can pose security risks and how the 802.1X standard helps address these issues by controlling network access. It's like having a bouncer at the door of a club, checking IDs to ensure only authorised individuals can enter.
Additionally, we have explored the role of EAP, which provides a flexible framework for determining who is allowed onto the network. When all these components are integrated, organisations can establish a robust security system that protects against potential threats and ensures the safety of their Wi-Fi networks for all users.
References