Smartly Detect and Crack Password Hashes using JohnTheRipper
No doubt hashcat is a good tool but what if you want to crack the encrypted document files like pdf or archive zip and smartly detect the hash type. John the ripper at your disposal for such things. You will learn about the basics of the JohnTheRipper suite in this post.
In the previous posts on hashcat, I have discussed hashcat and its feature with you. No doubt hashcat is fast and full of features for cracking the hashes. However, there are situations where you get encrypted files like zip archives or PDF documents where hashcat will fail to extract the password and crack it.
In today's post, I will share a very interesting project with you JohnTheRipper suite which consists of a main brute-forcing tool and set of utilities to extract the hash from files and then detect the hash itself during cracking. For more differences, you can refer to this post – https://www.reddit.com/r/crypto/comments/yuqyi/john_the_ripper_vs_oclhashcatlite/
LAB: Cracking Password of Zip Archive (Try it)
In this lab, you have a zip archive and a wordlist. Your objective is to break the password of the archive file and retrieve the file from it. If you were given the hash text, it would be easy to use the hashcat and this wordlist to break the hash.
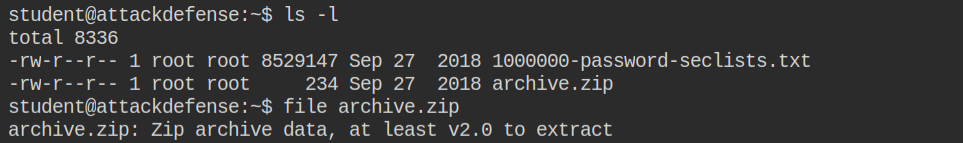
In this case, you only have a single target zip file. So you can use the zip2john utility to get the hash in the format of FILE_NAME:HASH. By default it will spit out on stdout, you can save this into a file using IO redirection zip2john archive.zip > hash
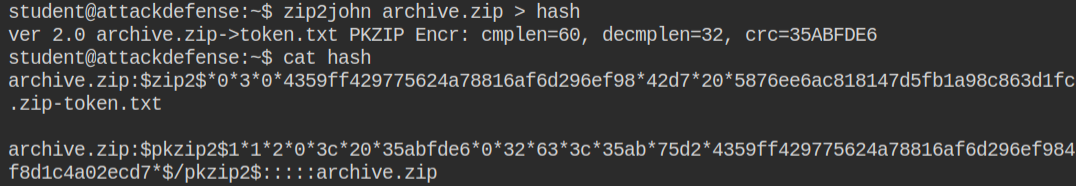
So now you have hash and wordlist file, all you need to do is to launch a dictionary attack using john by passing wordlist to the --wordlist argument followed by the hash file
john --wordlist=1000000-password-seclists.txt hashGive it few seconds to detect the type of hash and crack the password. You can see, it has already been identified the hash is WinZip and also other details like encryption (Sha-1) algorithm.
The password of the archive zip is midnight. Now you can use unzip or 7zip utility to unarchive this file and retrieve the secret file token.txt
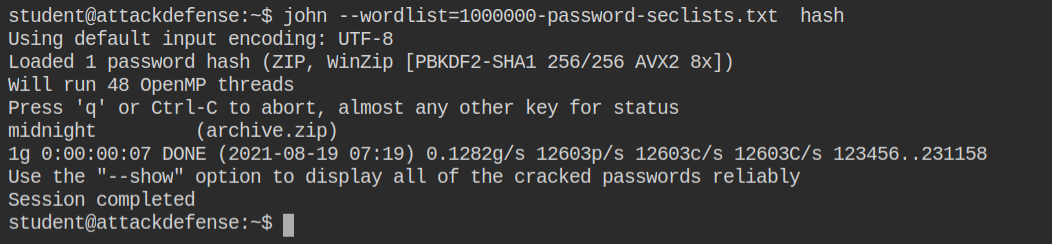
It will cache your password in the ~/.john/john.pot file. This will save time by simply printing the cracked password of the hash. You can use john --show hash to retrieve already cracked password from here
